|
Collections
in Cryptology - Paper
Alphabets |
|
|
Alphabetic
substitution ciphers exclusively on paper with no mechanical contrivances. |
|
|
The
Ché Guevara Cipher A double enciphered system (a straddling checkerboard and Vernam-type one-time key) cipher found with Ché Guevara when he was captured. It was used in this message fragment addressed to Fidel Castro dated May 18, 1967. Source: David Kahn, KAHN ON CODES, MacMillan, New York (1983). |
|
|
Compare this with Ana Montes' "straddling checkboard cipher."
|
|
|
A
Numerically Indexed Alphabetic Table It might be changed on a periodic schedule or used only once. For our purposes, let's index the letters with the line number first, then the column. |
|
 |
|
|
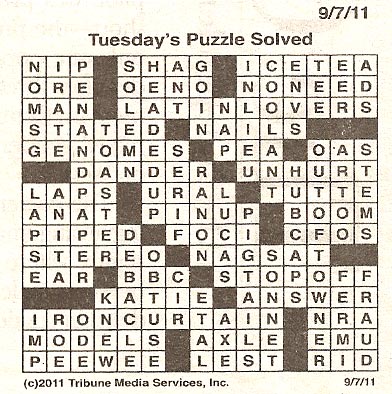
A
Candidate for a Pseudo-Random Key, Steganographically Hidden in Plain Sight The sender and receiver may secretly agree to use some widely published material as a daily key. It might be a newspaper article, letters or numbers read down a column on a page in a telephone book, or the low-order bits of pixels in an image on the Web. In this case, let's assume thatit's the daily solution to the DUKE CHRONICLE crossword puzzle: We might read it diagonally, up and to the right, beginning at the top-left corner: the letter "N." This would give us the following pseudo-random key: N OI MRP SAE GTNS..." |
|
 XXXXX XXXXX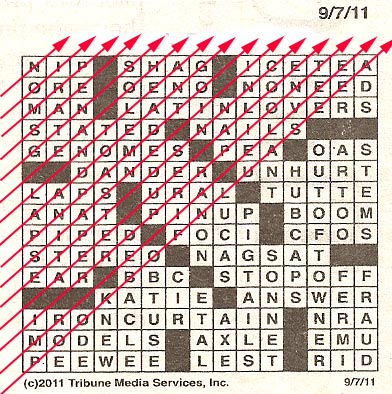 |
|
|
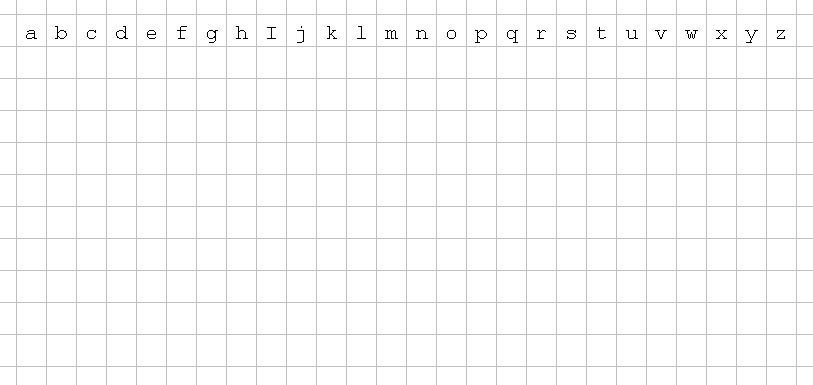
Polyalphabetic
Substitution A blank grid for encryption, decryption, cryptanalysis and demonstration purposes. |
|
 |
|
|
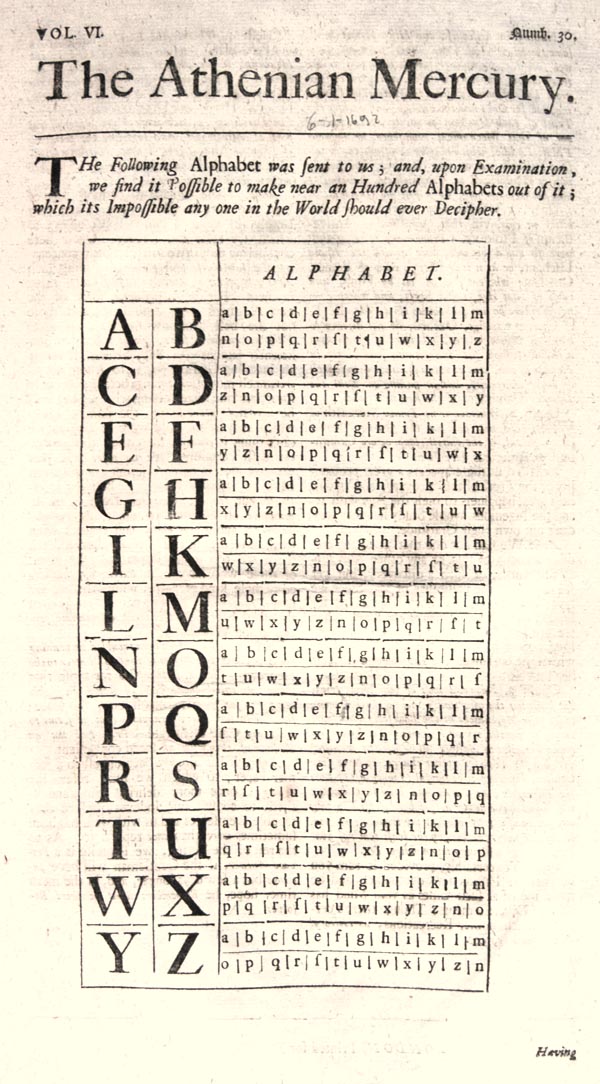
"near
an Hundred Alphabets" The Athenian Mercury (June 1, 1692) No "j" or "v" is used. No instructions were given. I count only 24 alphabets! Any ideas what the publishers had in mind? email me |
|
 |
|
|
|
|
|
To
encipher the password for a secret meeting. |
|
|
|
|
|
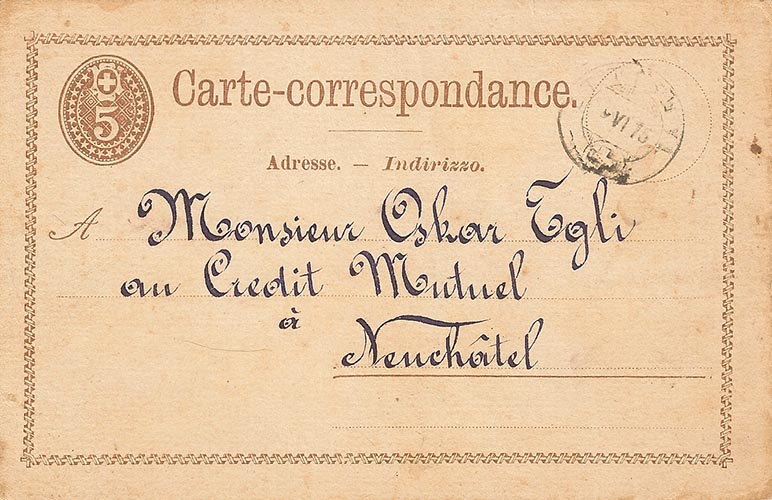
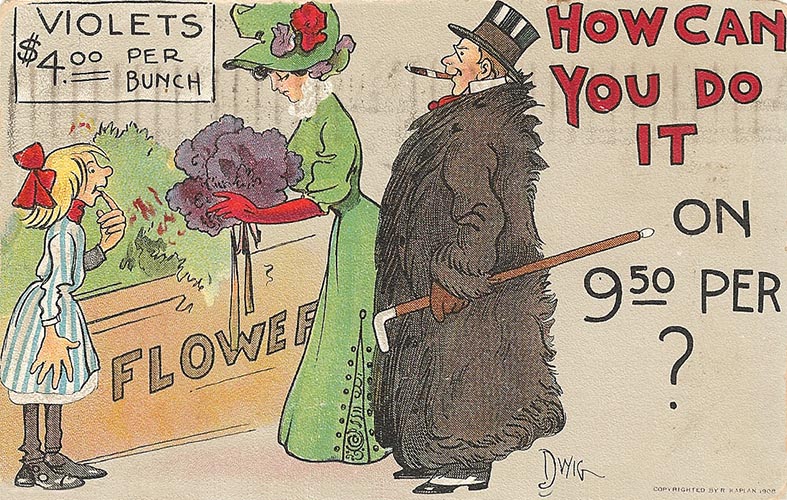
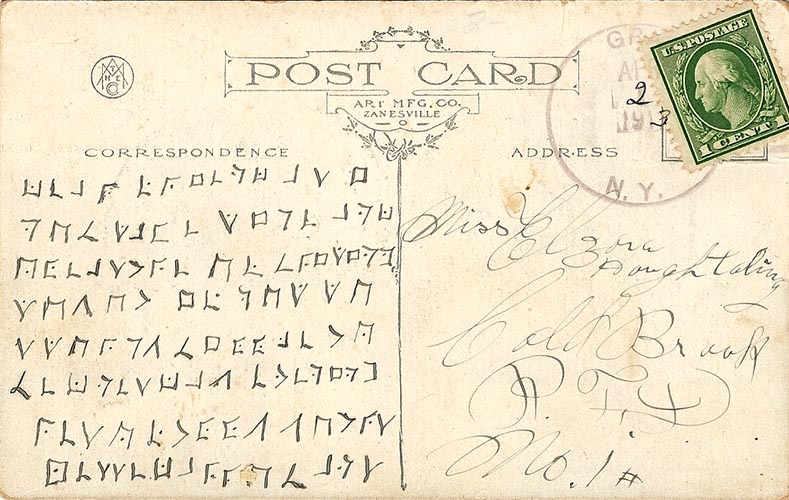
A) Coshocton 1907
Encrypted Post Card Hints for decipherment. |
|
|
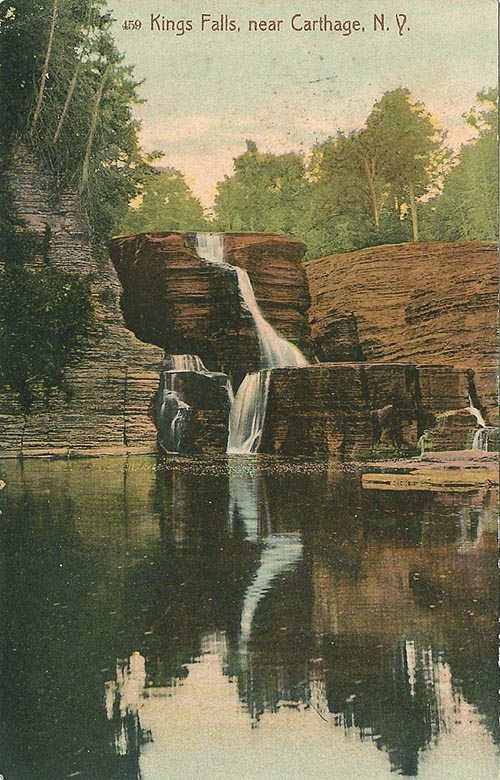
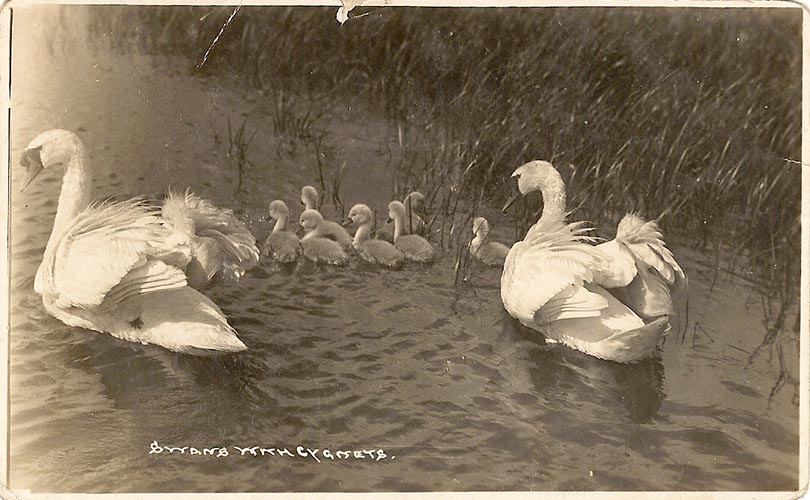
B) Carthage 1907
Encrypted Post Card |
|
 |
|
 |
|
C) Cobleskill 1906
Encrypted Post Card |
|
 |
|
 |
|
D) Santa Clara June 25
Encrypted Post Card |
|
 |
|
 |
|
|
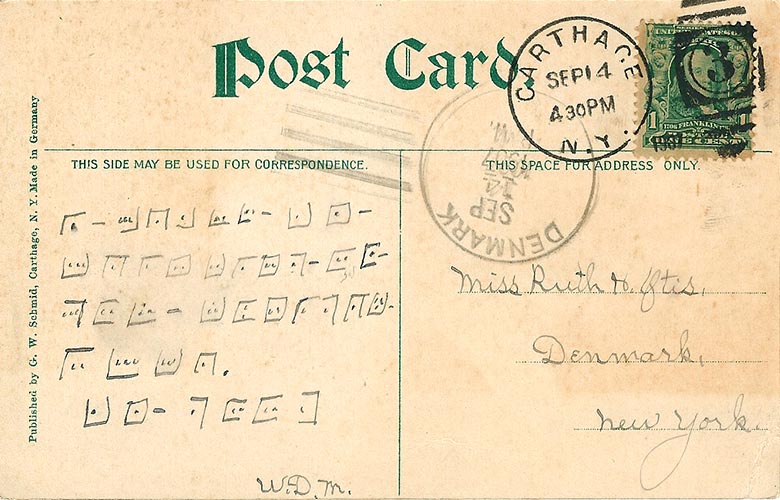
E) Neuchatel Swiss
Encrypted Post Card |
|
 |
|
 |
|
F) Hanford Encrypted
Post Card |
|
 |
|
 |
|
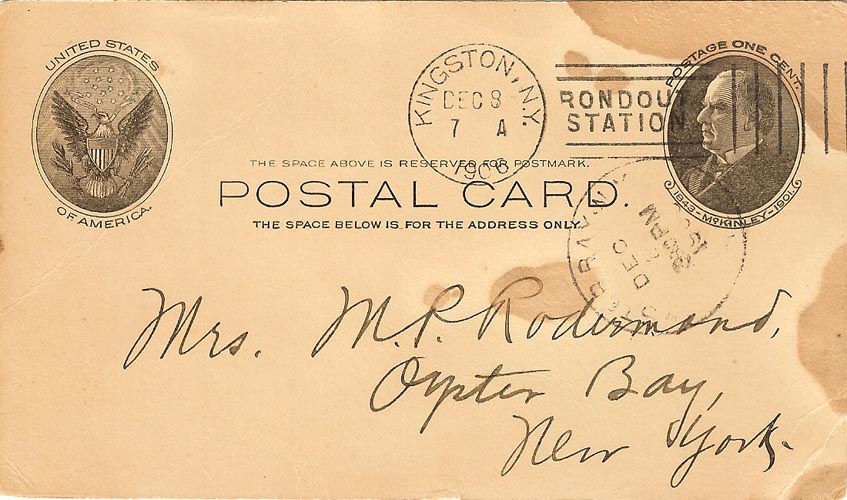
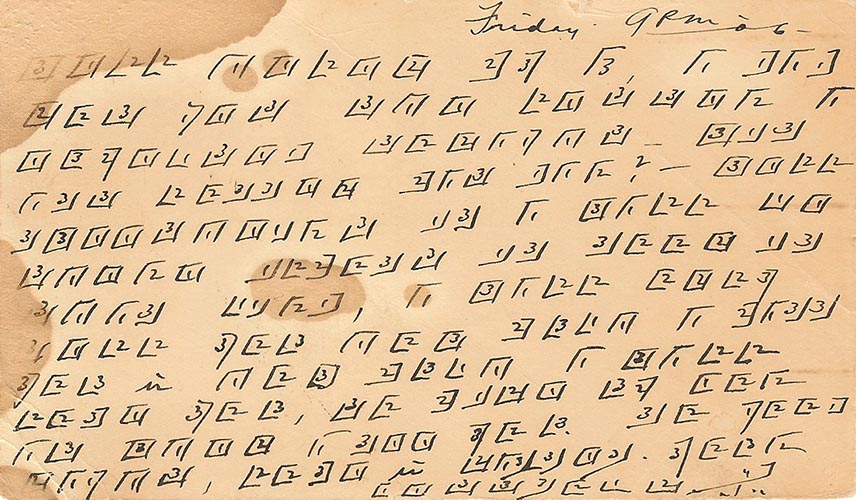
G) Kingston Encrypted
Post Card |
|
 |
|
 |
|
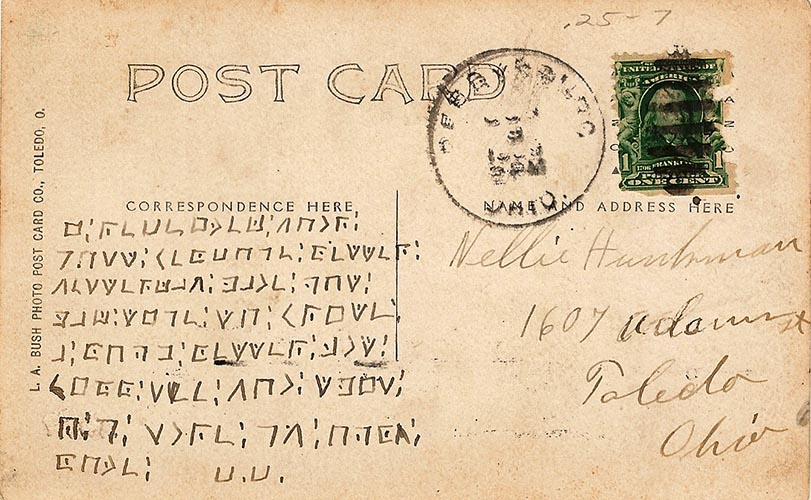
H) Toledo Encrypted
Post Card |
|
 |
|
 |
|
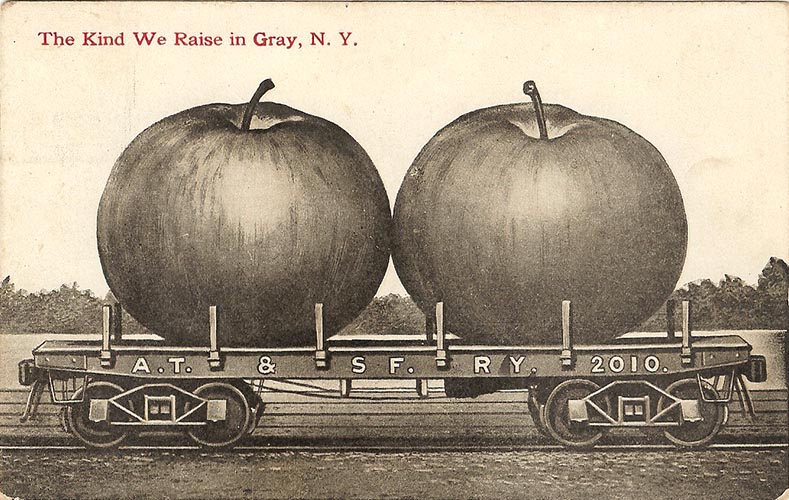
I) Gray Encrypted
Post Card |
|
 |
|
 |
|
J) London Encrypted
Post Card |
|
 |
|
 |
|
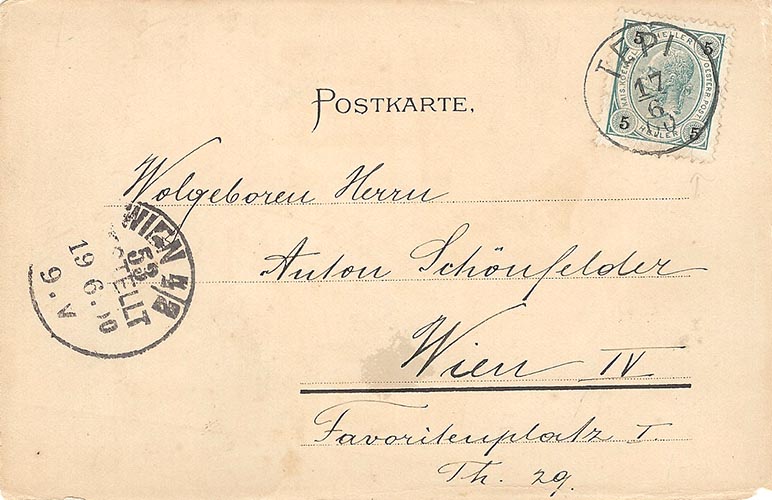
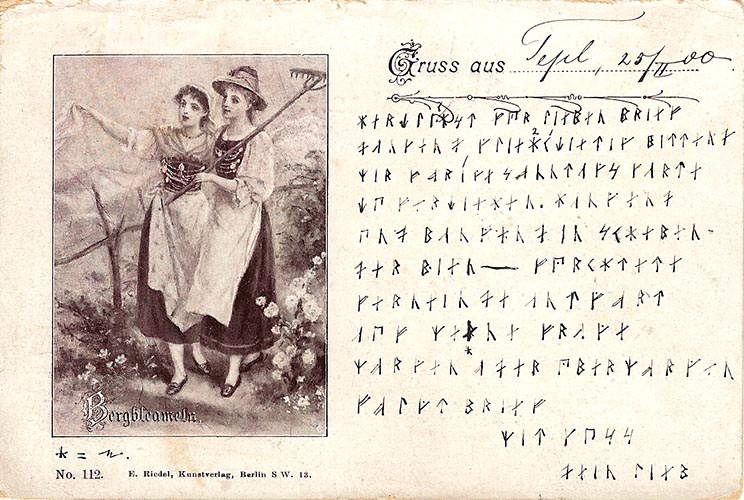
K) Tepi 17 Encrypted
Post Card |
|
 |
|
 |
|
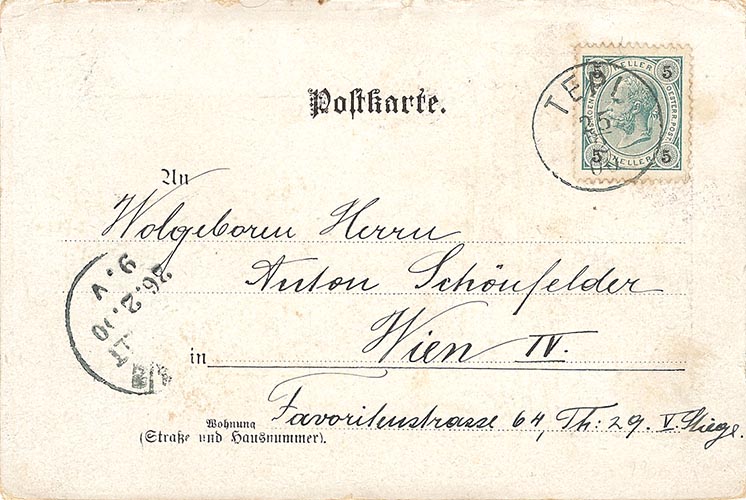
L) Tepi 25 Encrypted
Post Card |
|
 |
|
 |
|
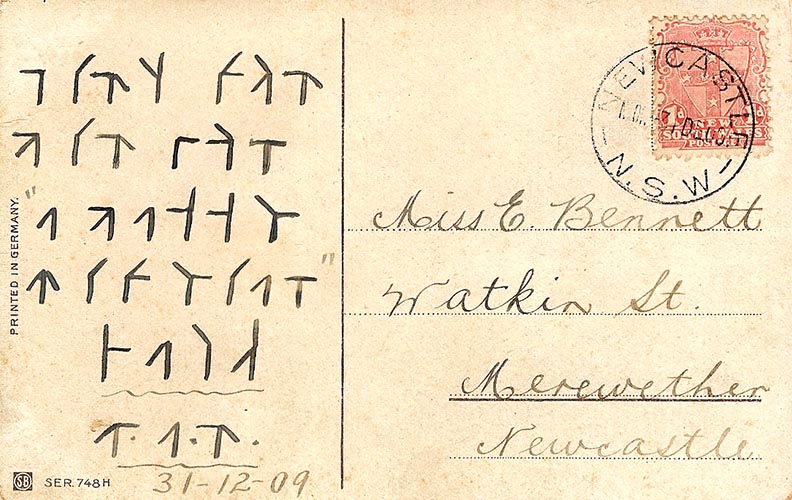
M) Newcastle Encrypted
Post Card |
|
 |
|
 |
|
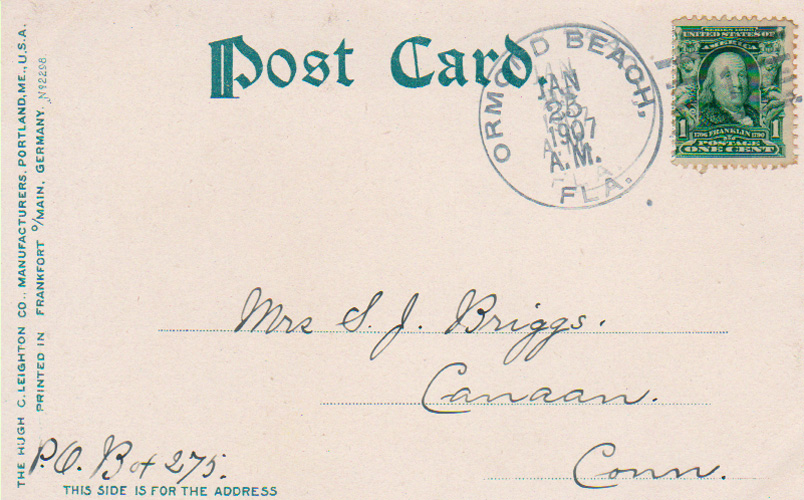
N) Ormond Beach Encrypted
Post Card (addressed to Briggs as in "O"). |
|
 |
|
 |
|
O) Paso Robles Encrypted
Post Card (addressed to Briggs as in "N"). |
|
 |
|
 |