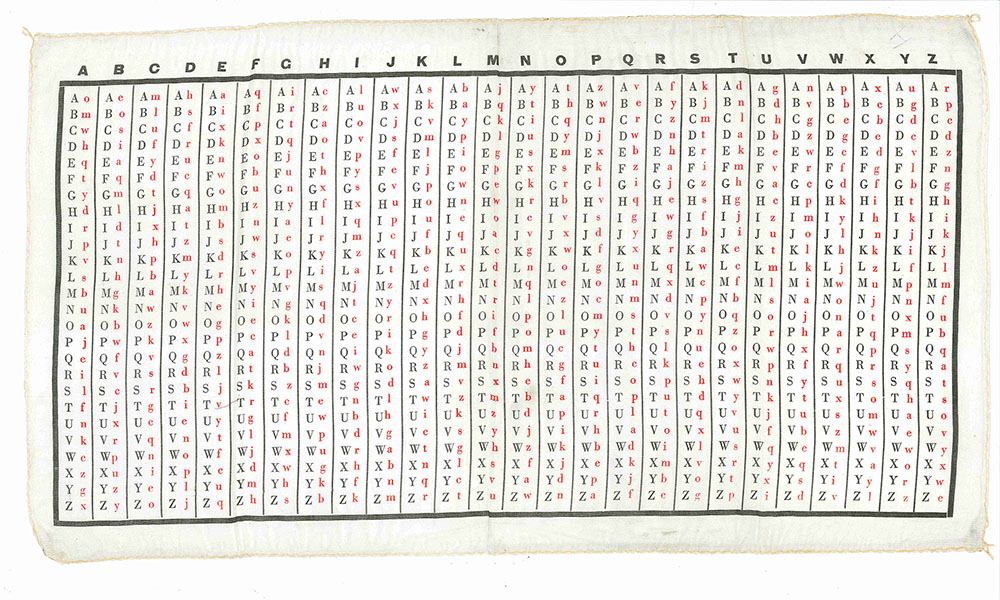
(A): British WW2 SOE (Special Operations Executive) silk table of 26 mixed alphabets.
A key-word would be sent secretly, perhaps hidden in a radio broadcast or a crossword puzzle, which would indicate the order in which the alphabets would be used.
If, for instance, the keyword was "PHOENIX," one would use alphabets P, H, O, E, N, I, X in sequence for each letter and repeat the keyword as often as necessary.
Assuming that cleartext is given in the black upper-case letters and ciphertext in the red lower-case letters, using the keyword "PHOENIX" we would enclode the cleartext "attack at dawn" as "zeaainxqotfl."
Click on the image for an enlargement.
John Brunner describes this as "a British One-Time-Pad conversion chart" (Brunner, OSS WEAPONS 1994, p. 205).